Serious Doubts: F-35 Stealth Fighter Faces Scrutiny Over Vulnerability in Active Conflict
Reports of a US F-35 being targeted in the Iran conflict have sparked debate over the stealth fighter’s vulnerabilities. Experts examine design limitations, radar detection, and modern warfare challenges.
F-35 Vulnerabilities Exposed? Experts Question Stealth Fighter’s Invincibility Amid Iran Conflict
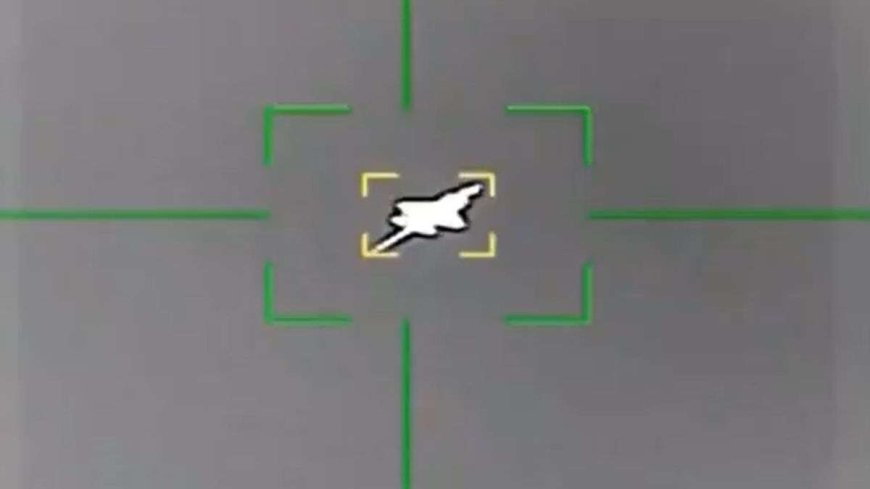
A recent development in the ongoing Iran–US conflict has raised serious questions about the perceived invincibility of America’s most advanced fighter jet, the F-35 Lightning II. Reports suggesting that Iran may have successfully targeted or damaged the stealth aircraft have sparked a deeper debate among defence experts about potential vulnerabilities in the jet’s design and battlefield performance. The F-35 is widely regarded as one of the most sophisticated combat aircraft ever built. Designed with stealth technology, advanced sensors, and network-centric warfare capabilities, it is meant to operate deep inside enemy territory while remaining largely undetectable. However, analysts point out that stealth does not mean complete invisibility. Instead, it reduces the aircraft’s radar signature, making it harder—but not impossible—to detect, especially under certain operational conditions.
One of the key limitations lies in the nature of stealth technology itself. The F-35 is optimised to evade high-frequency radar systems, but it can still be tracked by low-frequency radars, which some countries, including Iran, are believed to possess. These systems may not provide precise targeting data initially, but they can detect the presence of stealth aircraft and guide other weapons systems into position. This means that while the F-35 may not be locked onto directly by fire-control radar, its general location can be identified, allowing adversaries to deploy anti-aircraft assets or scramble interceptors in response.
Another factor is mission profile. When stealth jets fly repeated sorties over the same region, adversaries can begin to identify patterns in their movement. Over time, this allows air defence systems to anticipate flight paths and deploy countermeasures more effectively. In a prolonged conflict like the current one, such predictability can reduce the advantage of stealth. Iranian forces, having faced sustained aerial operations, have had the opportunity to study US flight patterns and adjust their radar coverage and missile placements accordingly, potentially increasing their chances of a successful engagement.
External payloads also play a role. While the F-35 is designed to carry weapons internally to maintain its low radar visibility, certain missions may require additional external payloads. When this happens, the aircraft’s stealth characteristics are compromised, making it more detectable to enemy radar systems. Hardpoints, fuel tanks, and weapons mounted externally create radar reflections that can significantly increase the jet’s visibility, turning a stealth platform into one that resembles a conventional fighter in terms of radar signature.
Electronic warfare is another area where vulnerabilities can emerge. Although the F-35 is equipped with advanced electronic countermeasures, modern battlefields increasingly feature sophisticated jamming and signal-disruption technologies. Iran, for instance, has invested heavily in electronic warfare capabilities, which could interfere with the jet’s sensors, communications, or navigation systems. Disruption of the F-35’s sensor fusion—the very feature that gives it its battlefield awareness advantage—could degrade its ability to detect and respond to threats in real time.
Speed and manoeuvrability have also been discussed as relative limitations. Unlike older fighter jets built for high-speed dogfights, the F-35 prioritises stealth and sensor integration over raw speed. While this is not necessarily a disadvantage in modern warfare, it can become a factor in situations where quick evasive action is required against incoming threats. In scenarios where stealth has been compromised, the F-35’s agility—while capable—does not match that of dedicated air superiority fighters like the F-22 Raptor, potentially leaving it at a disadvantage in close-range engagements.
Importantly, the current conflict environment itself is highly complex. Iran’s strategy has relied on layered air defence systems, combining surface-to-air missiles, drones, and radar networks. This multi-layered approach increases the chances of detecting and engaging even advanced aircraft. In fact, reports indicate that Iran has successfully targeted several aerial assets, including drones, during the conflict. Recent reports also suggest that a US F-35 may have been damaged during a mission over Iran, forcing an emergency landing—an incident that, if confirmed, would mark a significant moment in the war. While investigations are ongoing, the possibility alone has been enough to trigger global discussions about the aircraft’s real-world performance in contested environments.
Also Read: Meta Considers Major Workforce Cuts as Billions in AI Investment Reshape the Company
Experts caution, however, that no military system is flawless. Even the most advanced platforms are designed with trade-offs, balancing stealth, firepower, range, and survivability. The F-35 remains a highly capable aircraft, but incidents like this highlight that its effectiveness depends heavily on how it is deployed and the nature of the threat environment. Ultimately, the reported incident underscores a broader reality of modern warfare: technological superiority does not guarantee immunity. As adversaries continue to develop countermeasures, even cutting-edge systems like the F-35 face evolving challenges. As the conflict continues, analysts will be closely watching how both sides adapt. Whether this episode represents a rare occurrence or a sign of shifting dynamics in aerial combat, it has already added a new layer of complexity to the ongoing war—and raised important questions about the future of stealth technology in an era of increasingly sophisticated air defences.